March’s meeting was filled with all sorts of shenanigans. dw5304 started things off with a little demo of Windows Server 8 and some of its improved features and functions.
Ngharo kept the OS ball rolling by going over some Linux 101 and while he was showing us how grep can be used to find wanted data in Apache logs Castor pulled a little prank on Ngharo and left a message in the logs for him 😛 Every one got a big laugh out of it. Ngharo also has promised to give a new Linux demo every meeting!
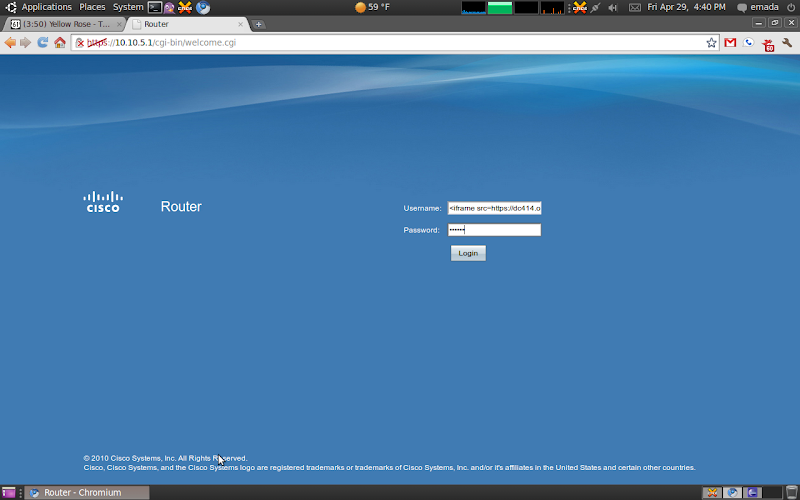
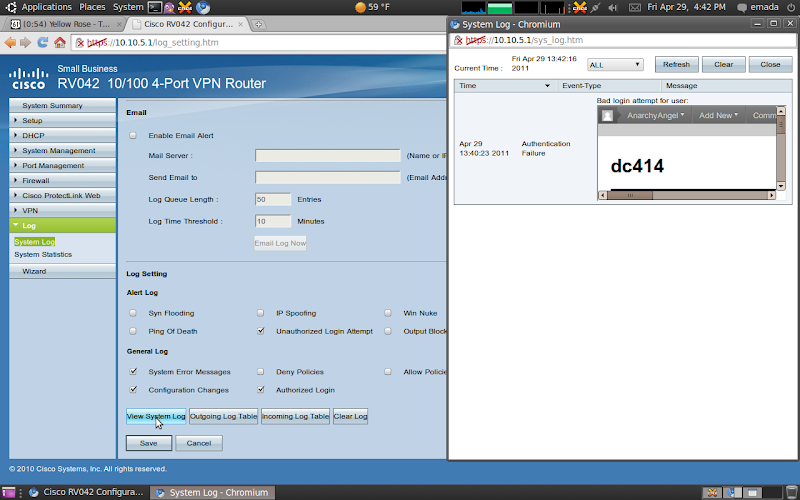
Then I stepped in and gave a demo on how to use temp XSS attacks to gain access to user accounts on web sites, the target in this case was Daily Motion using a known vector. It was complete with a explanation of the attack string, the payload, how to use it, and how to fix it. I gave the room the opportunity to hack my Daily Motion account, using the cookie stolen during my demo which turned out to be a bad idea, Ngharo thought it was cute to replace my profile picture with the index picture from lemonparty2 😐 Yeah, ok I loled hard at that one 🙂
Then The Professor showed us how to use “The Social Engineering Tool Kit” to phish n00bs and pwn their passwords! He gave us a step by step of how to copy a website, how to access the phish page, and what happens when its used. Then we all talked about how to know when your being phished. It was a great first demo from The Professor.
A big congrats to The Professor for winning the dc414 Free Junk Giveaway “pic below”, Enjoy your new Launchpad 🙂 Here are some other pictures from the awesome Cmoney.
The big winner:

SIDE NOTE:
The next morning with a slight hangover I open my email and find this from Daily Motion:
Hello anarchyang31,
The avatar of your Dailymotion account “anarchyang31” has been deleted due to non respect of the General Terms Of Use (inappropriate content).
In any event, we ask that you observe those conditions. You can review them by clicking here: http://www.dailymotion.com/legal/terms
After 5 deleted avatars, you will no longer be able to change it and it will be replaced with a default avatar.
You can upload a new avatar by clicking here: http://www.dailymotion.com/profile/avatar
Best regards,
—
The Dailymotion Team
LMAO thanx Ngharo. Ok thats it, later.