dc414 and I are proud to introduce Upnp Exploiter! A Upnp scanner and exploit tool. This tool comes with two main scanning functions and exploit functions.
The first scanning functions is the target scan. Here you can pick a single IP or IP range to find anything that reports back to a UPNP multicast packet sent to the normal UPNP broadcast address “239.255.255.250 on port 1900” If target responds it takes a closer look and sees if it can get the targets UPNP profile letting us know what type of device it is, what UPNP functions it supports, its IP, and other information. When used remotely, this all takes advantage of the fact that the target device violates the UPNP specs and responds to UPNP requests outside of the deices local area network.
The second scanning function only works in a local area network and just sends out a UPNP broadcast. This function is just using the UPNP protocol as intended.
Once a list of UPNP supported devices are found the script mines some information from it like device type, UPNP functions, IP. If its a gateway device it prompts you and asks if you want to attempt to exploit it.
The first option is to forward ports. If doing this LAN side its best to do some network recon with NMAP or something, find some fun services running on a internal server and forward them to the web for later hacking. While gathering information on the device it gets a list of other ports forwarded via UPNP and the devices internal IP. This is supper helpful when doing things on the remote side. One of my personal favs is routing the modems internal port 80 to 81 on WAN. This should give you access to the routers internal web UI for configuration. Most of the time the default creds will work for admin access >:)
This of course violates lots of rfc’s, protocols, and other stuff lol.
The second exploit option tries to turn a gateway device into a proxy. Now this works using IP addresses and one host per port. So if you want to connect to Victim A on port 8 you use the script to forward all data coming in on any port you choose “for now we will say 88” to VA on port 80. So you connect to port 88 on the Victim B “the gateway device” and all the traffic is forwarded to VA on port 80. This also breaks UPNP rules, but who cares.
The last little thing this script does is parse the replies for the unique_service_name() vulnerability and reports to you if it finds anything with some helpful information to aid in exploiting it.
You can get the script from the git page HERE. If you like it please consider donating to dc414 or me (Anarchy Angel – anarchy@new.dc414.org) for taking the time to make such an awesome script 🙂 If anyone would like to help with development please contact Anarchy Angel (me).
Many thanks to Ngharo for help with the regex and list stuff.

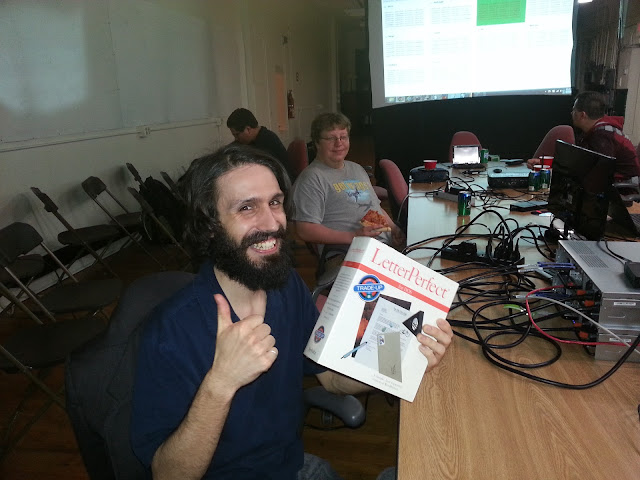 edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC!
edgewalker was one of the lucky contestants to win the Free Junk Giveaway. Enjoy the LetterPerfect software on your IBM/DOS compatible PC! 

