Whoa. A meeting recap.
So what did we all do?
Caleb – Presented on Crafting Digital Radio Signals, to Control Things
He has a blog post about his Digital Radio Signals, and that was a majority of what was presented. He was able to do a live demo of the capture of a remote outlet, and replay of the capture.
There was also “a peculiar signal hiccup”, wherein the signal to the remote outlet would not be received. It would be similar to a jamming signal, if jamming radio signals were allowed. Good thing we abide by all RF rules.
He demonstrated the ability to observe vehicle remote locking, and showed the lock and unlock signal.
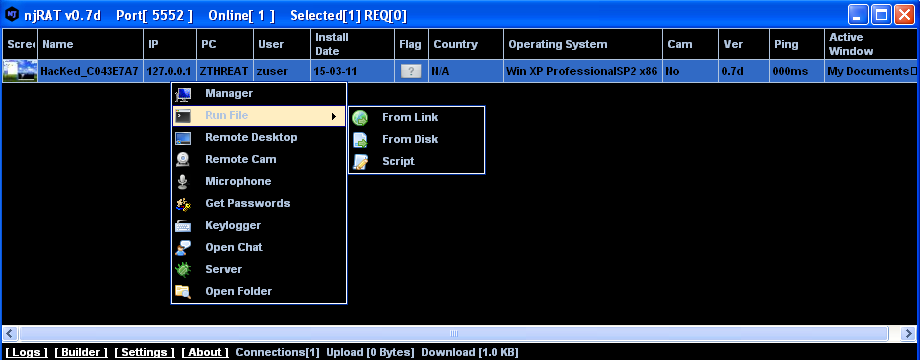
njRAT v0.7d – Part Two
A part two would make sense with part one, but ::shrug::
Showed off the njRAT v0.7d that came along for the ride on a torrent. njRAT is a remote-access Trojan that has been used for the last few years. A 2013 report from General Dynamics / Fidelis Cybersecurity Solutions goes over detailed indicators, domains, and TTP’s in conjunction with attacks using njRAT. It is also apparently up to version 0.9. The malware is making a comeback, and maybe due to some evasion techniques shown. (or people just continue to be dumb in downloading from torrents. That could be it too)
If njRAT is run, Hey, Look! It’s detected as a virus!
Instead, do some tech magic (someone can add detail) using Base64 in Microsoft Visual Studio. Runs now, the EXE is loaded, and it doesn’t trigger alerts or errors.
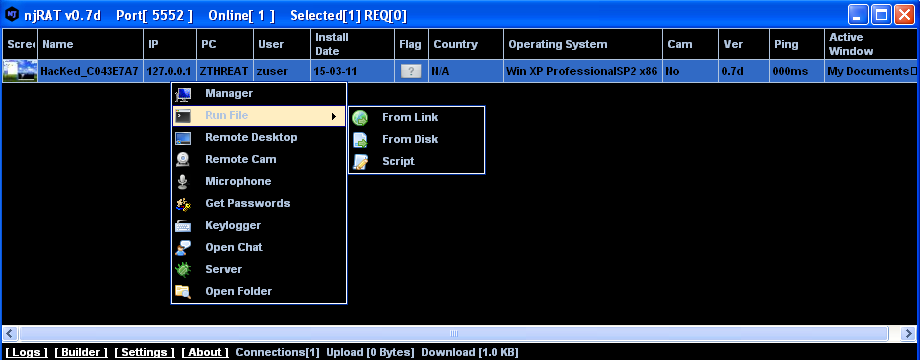
And hey, we have a remote desktop!
If we turn on the remote webcam function…
…hey! This is why you should tape over your webcams! And we had keyloggers, microphone access, and chats available too!
So, just don’t trust things that are pirated from the Interwebz.
Do you want this for yourself? Do a search for njRAT or njRAT v0.7d, and you can have it yourself. (or, it seems 0.9 is around) You will have to compile/tinker/tech magic it yourself, though.
Picking on Level 3
Well, not directly. We were shown a few links to see Internet health
Dynatrace , Dynatrace Keynote, and DownDetector
We just couldn’t help noticing how bad Level3 looked at the time.
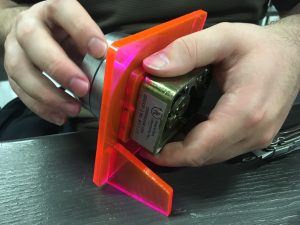
Hacking the HooToo HT-TM05
So this is a $40 Travel Router, and we can HACK THE SHIT OUT OF IT

Has WiFi built in, (added?) a 128GBD SSD, and it has a full Linux kernel on it now, OpenWRT, and Powered by LuCi. Portable power that also lasts a good portion of the day.
Can do a File Server, put movies onto it, or put a web forum on it. We plan to set one or more of these up and carry them around DEFCON 25.
Relevant GitHub that may be useful
Some were also interested in the PirateBox , that can be built on different hardware for about $35.
Something something CYPHERCON
Yeah. See @cyphercon or cyphercon.com if you have no clue here.
If you have a better recollection of things from our meeting, good for you! Also, we could probably use that info in this update. Comment or edit, or e-mail some DC414 folk about your contributions.